- cross-posted to:
- [email protected]
- cross-posted to:
- [email protected]
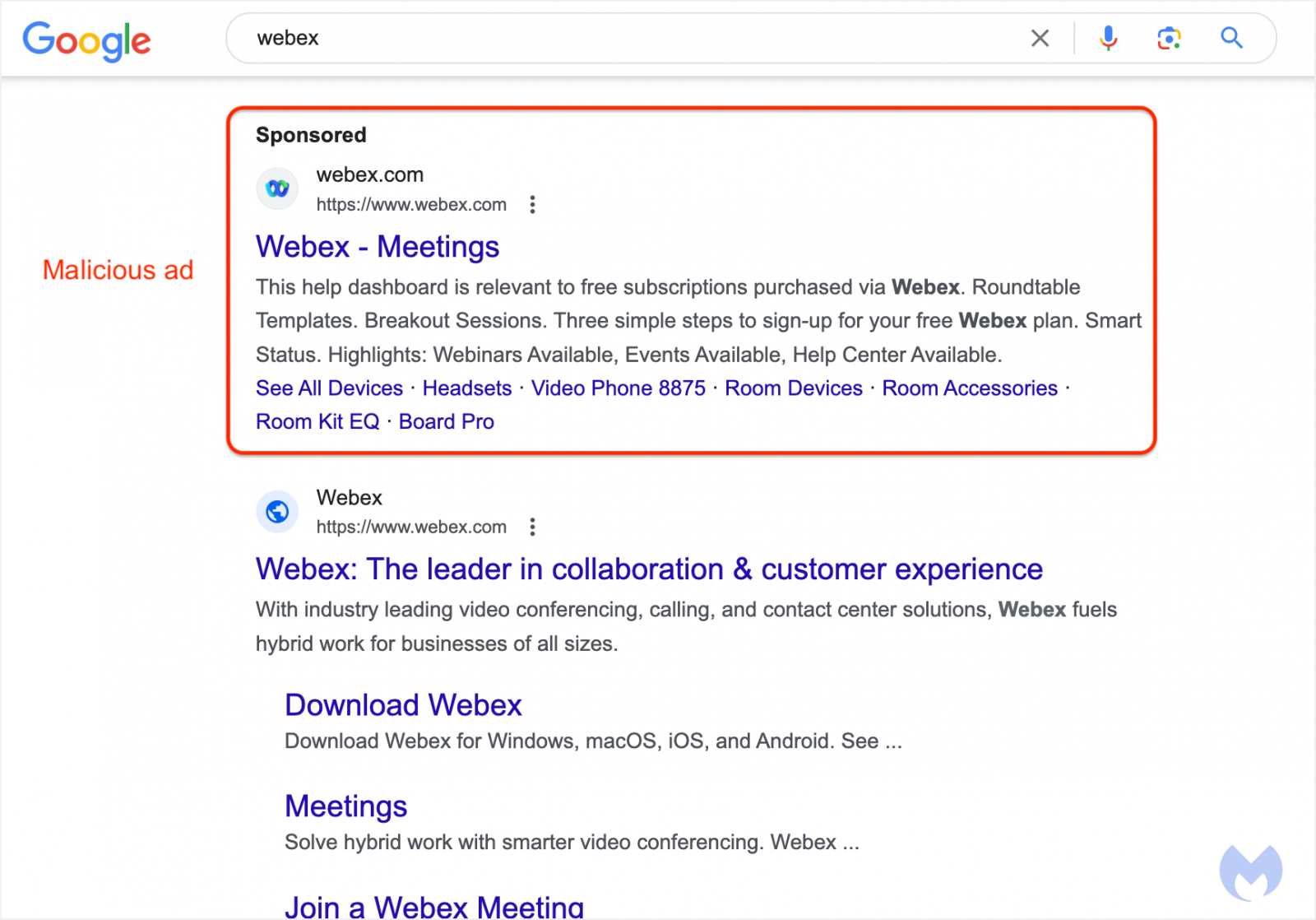
Most people know at this point that when searching for a popular software package to download, you should be very careful to avoid clicking on any of the search ads that appear, as this has become an extremely common vector for distributing malware to unsuspecting users.
If you thought that you could identify these malicious ads by checking the URL below the ad to see if it directs to the legitimate site, think again! Malware advertisers have found a way to use Google’s Ad platform to fake the URL shown with the ad to make it appear like a legitimate ad for the product when in fact, clicking the ad will redirect to an attacker controlled site serving malware.
Don’t click on search ads or, even better, use an ad-blocker so that you never see them in the first place!
Businesses should not be allowed to serve ads from random people without curating/checking them first. Yeah it would be a lot of trouble and cost a lot of money, too fucking bad you are making billions of dollars off this.
Yeah seriously, they can and should have a team dedicated to approving ads.
And if False Advertising is a crime in print media, why is malware advertising not also a crime?
It probably is a crime, but large corporations don’t have to care about crimes because they can just pay the fines and be on their way like nothing happened. It’s no more of an inconvenience to them than just a small mosquito landing on them.
If False Advertising in web/app ads started being prosecuted, the whole Internet economy would be devastated. Would probably be thousands of dollars per violation. Just think of all the scummy ads that appear on news sites or in apps. I even consider those “Download Now” button type ads to be false advertising, they are trying to look like part of the page they are served on, they don’t even tell you what you’re downloading.
I think there’s a difference between scummy ads like false advertising which is obviously bad, and downright malicious software which it sounds like the ad OP is talking about serves actual malware.
You may find such things in similar contexts, though I would believe that an ad service willing to serve either would hammer you faster for malicious payloads than confusing download advertisement misdirects.
I should probably read the article. If the title isn’t misleading, it is possible to use google referral urls as a masking service and pay for visibility on the link :/
Because Google has gotten the law steuctured such that THEY aren’t liable for false advertisements they host and serve.
If I posted an ad that was blatantly false on Google, legally I’m the one liable, not Google.
It’s ass backwards, Google should be on the hook for this and should have to curate advertisements. Especially when so any of them are not just fake but are openly malicious
Google search has become such garbage.
Use duckduckgo -> duck.com
I don’t get why anyone is still using Google in 2023.
At least not without an ad blocker. I never see these ads, but if I did I would initially assume they were generally safe being served by Google and right at the top of the search results. There is no excuse for this, yes users need to be careful but Google should never serve this deceptive crap to begin with.
This has been a feature of Google Ads forever. It isn’t even “found a way” it is just a box to fill in the ad manager.
Presumably this is so that they can use tracking links to analyze the performance of the ad without making the URL “ugly”. But it is easy to abuse. (Although I think Google attempts to do some checks, but of course those are always going to be unreliable.)
Presumably you can hover over the link to see the actual URL (which I think is best practice anyway), or is it more sophisticated than that?
AFAIK even legitimate ad clicks will first direct to an analytics platform before redirecting to the destination site, so that they can track click through rates and where the referral came from. So it is unlikely that ad links will actually go to the website you expect them to even in normal scenarios. It is actually this mechanism that the malicious ads described in the article are using to fake the display URL.
I would always out of habit avoid any links that go to somewhere other than the advertised destination - so if it goes to an analytics platform I would copy and paste the text if the text of the link is a URL, or find an alternative. Always hovering links and being absolutely sure of where they go should really be taught as standard practice.
I always check the status bar but I actually noticed the other day on LinkedIn or maybe Facebook, that the status bar said one thing, but the link was different,
E.g the hover over said https://website.com but the actual link was something like https://linkedin.com/linkout/wbdjdhgaj?user=xhedb
That type of thing is concerning. What browser are you using out of interest?
Sorry for the slow reply, but it was a link on LinkedIn and I’m using chrome. It’s frustrating as I use the status bar to check the link is the same as the text before clicking it.
deleted by creator
Just double checked and this also happens in Firefox. I think the other user in this thread has explained it well, looks like a JavaScript intercept onClick to prevent the link action and instead call a JavaScript function to open a different link.
In this case it is built into the site so I guess it is OK on the basis that I am trusting LinkedIn to not do anything malicious but it was more the principle as I had previously looked at the status bar to confirm the link was what I was expecting but in the future I will be more wary. Interestingly, right clicking and selecting “copy link” does actually copy the page which is loaded as opposed to the one on the status bar.
If you have linkedin it seems to be links in direct messages if you would like to see yourself.
That’s trivial to do where you control the link text. For example: https://www.google.com/
Sorry, I don’t mean the link text itself, but the destination shown in the status bar in the bottom left of my desktop browser.
Yeah that shouldn’t be possible on a platform like LInkedin or Facebook. If it’s a site you control, though, it’s still easy. I can’t do it here (at least I hope I can’t) but here’s an example of it: https://jsfiddle.net/z2pLaxto/1/
Yes, that looks exactly like what is happening. For clarity though it is a LinkedIn script not one uploaded by a 3rd party.
It seems to apply to links sent in direct messages which are routed through a linkedin internal page, I assume so they can track you out etc.
It was more the principal of it though, I hadn’t considered that the link shown in the status bar could not be the link you would be taken to if you click it but I guess that’s part of allowing javascript to run.
Had this happen searching for Argos (a large British retailer). The sponsored result sent me to a survey scam that cloned the Argos site, quickly reported it.






