- cross-posted to:
- [email protected]
- cross-posted to:
- [email protected]
cross-posted from: https://lemmy.ml/post/4912712
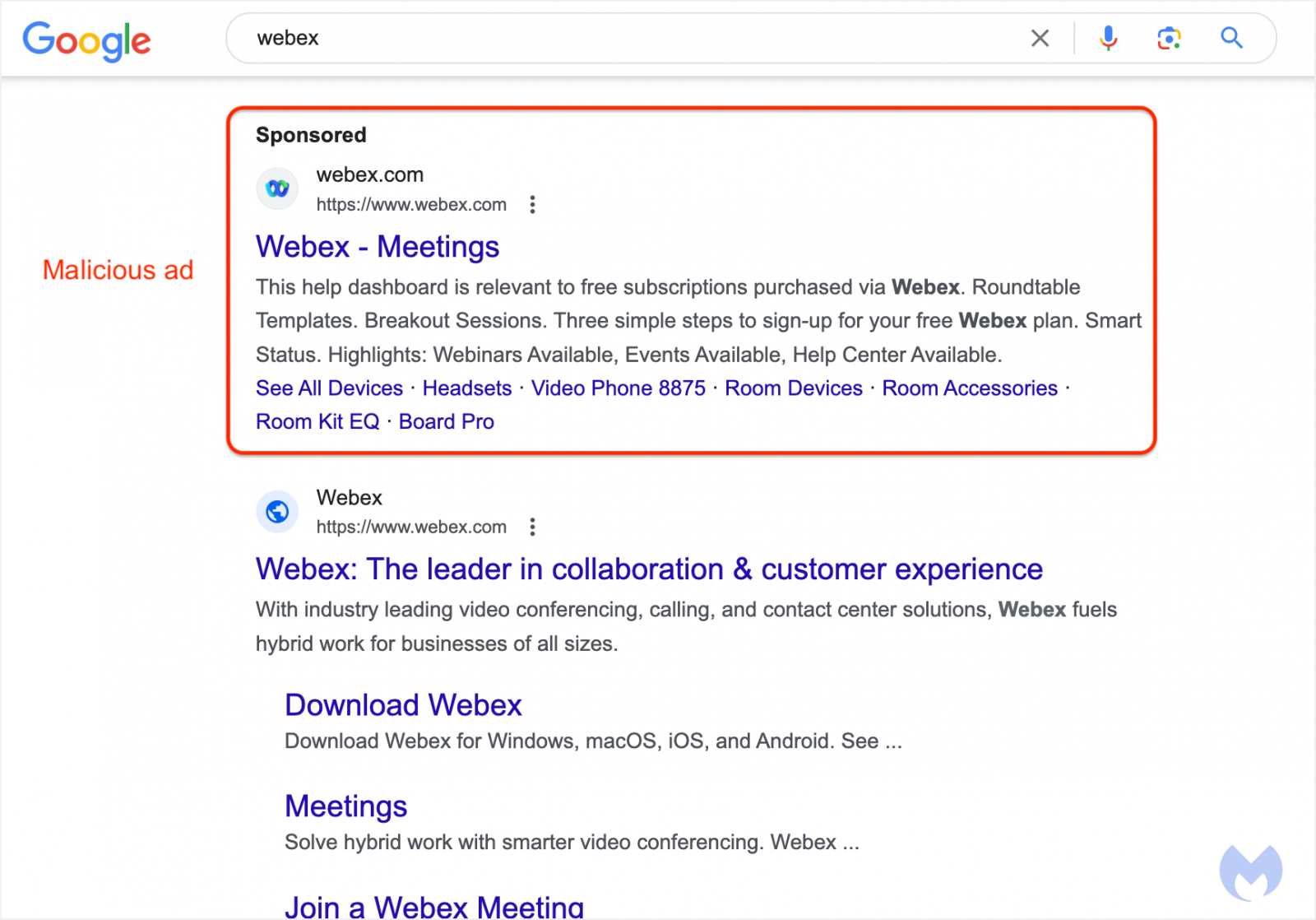
Most people know at this point that when searching for a popular software package to download, you should be very careful to avoid clicking on any of the search ads that appear, as this has become an extremely common vector for distributing malware to unsuspecting users.
If you thought that you could identify these malicious ads by checking the URL below the ad to see if it directs to the legitimate site, think again! Malware advertisers have found a way to use Google’s Ad platform to fake the URL shown with the ad to make it appear like a legitimate ad for the product when in fact, clicking the ad will redirect to an attacker controlled site serving malware.
Don’t click on search ads or, even better, use an ad-blocker so that you never see them in the first place!



Don’t use google search, if you do, do not follow ‘sponsered’ links. Not only may they be malware, as in this case, but google will be tracking you.
It’s truly amazing that google gives no fucks whatsoever when it comes to ads, yet their threat security team is one of the best in the business.
After works drinks must be fun…
I remember my coworkers (who were devs) Google searched Firefox to download and hit the first link which was an ad. It was a German version of Firefox with spyware.
Our IT department caught it but I was sorta surprised my coworkers hit the link as opposed to the first search term. That ad was active for a long time though … I think years.
Google tracked the other links too.
So there’s that
Google tracks you everywhere, particularly with captcha. If you block connection to google.com and gstatic.com then half of the internet won’t work.
I can’t believe we’ve gotten to the point where running random code on your computer isn’t just considered normal, we also think blocking said random code is bad for business.
I’ve been using a SearXNG locally-hosted instance using WSL/Podman. Behind a VPN of course; and also using TrackMeNot to generate a steady slow stream of garbage searches to block general query tracking.
I’m loving it to bits; as I don’t have bullshit in my search results and I immediately find what I need; as I can query all the engines I want.
Is it easy to self host SearXNG? What is the minimum requirements needed to self host?
I don’t know the exact requirements but I’m literally running a locally hosted one on a much more previous generation CPU (i7-7820HK) and I appear to be using no more than 4GB of ram including Podman Desktop, WSL and the Docker image itself not seeming to consume that much RAM.
I don’t feel as if you could possibly lack the system resources needed to do it comfortably if you have at least 12GB of ram (for locally hosting on Windows 10) or 4GB of ram (Any flavor of Linux probably, if you wanna throw an old PC or rPi/rPi-like at it.)
You should look closely at https://github.com/searxng/searxng and find out what the exact requirements could be by asking the maintainers.
Just another +1 reasons to use ad block.
Ecosia plants trees while Google gives you tech-disease.
Man I would love it if Ecosia actually had decent search results. Well, guess I’ll have to donate for trees.
Ecosia uses Bing, so it’s probably good for porn. Google has gotten worse lately anyway, so half the time adding a !g bang doesn’t actually help.
Yeah Ecosia probably uses the free google api and not the paid one. I use SearX. Wonderful little search engine.
deleted by creator
deleted by creator
deleted by creator
Use pihole. If I accidentally click a google ad they don’t work anyway.
I have them blocked in the host file on my router
But I was assured by IT pros that responsibility to stop phishing tested ultimately on the user!